Reverse Engineering Coin Hunt World's Binary Protocol | NCC Group Research Blog | Making the world safer and more secure

A CBAM‐GAN‐based method for super‐resolution reconstruction of remote sensing image - Wang - IET Image Processing - Wiley Online Library

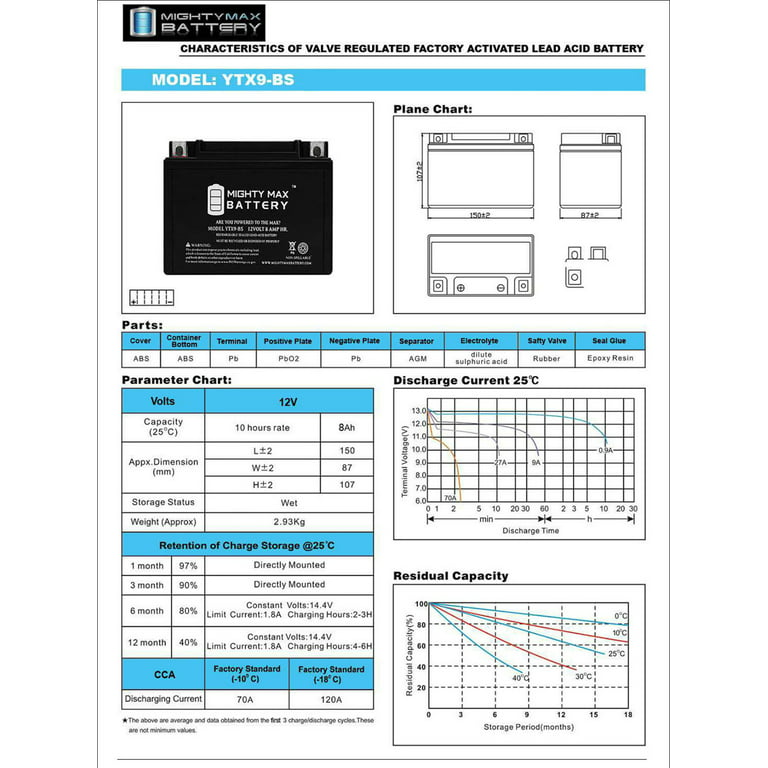
Sensors | Free Full-Text | Optimal Energy Management System of IoT-Enabled Large Building Considering Electric Vehicle Scheduling, Distributed Resources, and Demand Response Schemes
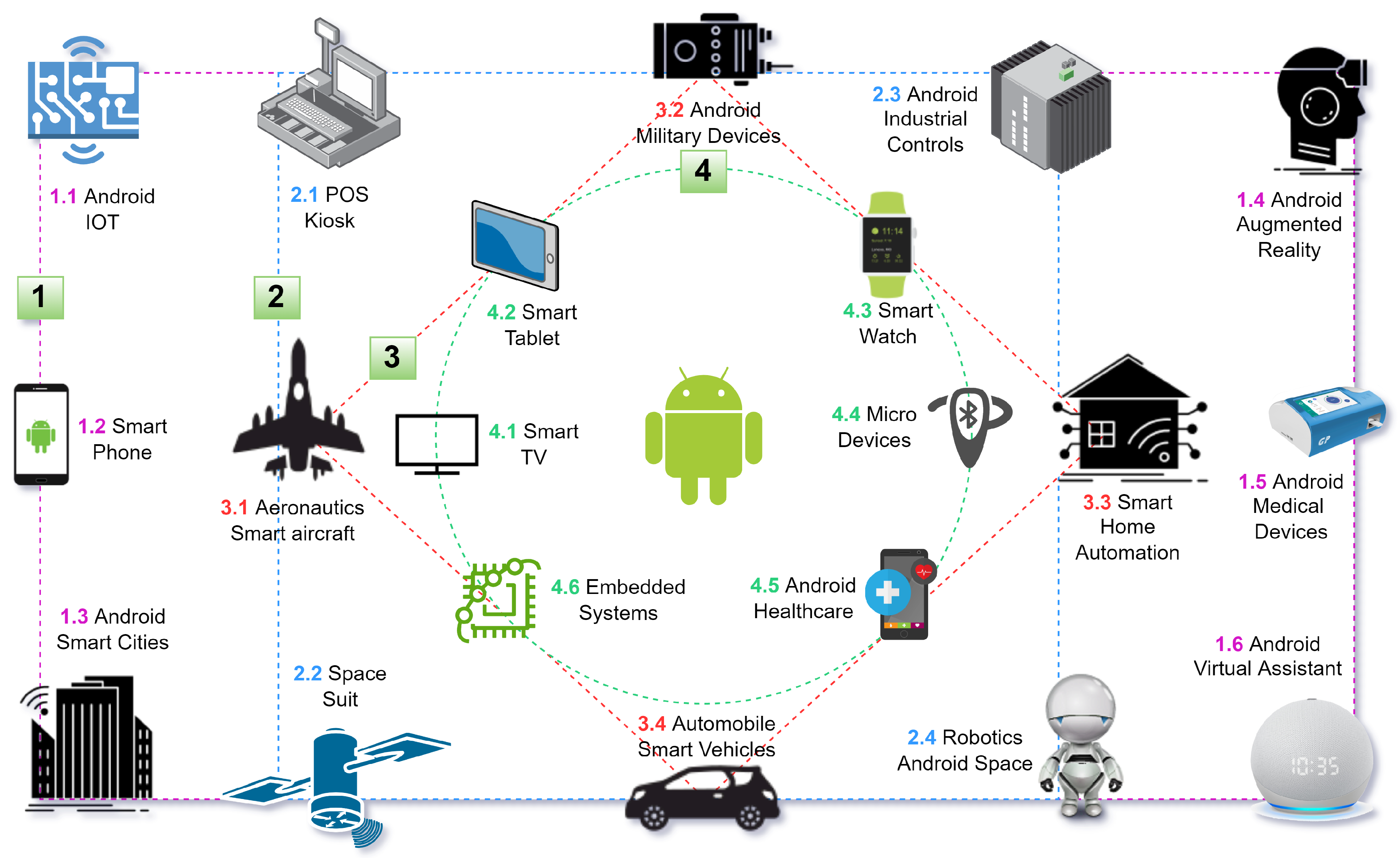
Technologies | Free Full-Text | Smartphone Security and Privacy: A Survey on APTs, Sensor-Based Attacks, Side-Channel Attacks, Google Play Attacks, and Defenses